
A large number of Android manufacturers (OEMs) are skipping security patches but are lying to users about it, according to the team at Security Research Lab (SRL), a Berlin-based cyber-security firm.
Google releases Android security patches each month in the form of the Android Security Bulletin. The OS maker releases the security bulletin to OEMs and chipset providers, and each add their own updates, depending on the Android OS variation that ships with each smartphone.
Every time any of these updated OS versions reaches a user's device, the update also increments the "Android security patch level" in the phone's settings section to the respective month and year of the Google Android security bulletin they have implemented patches for.
Some OEMs are slacking off
But speaking today at the HackInTheBox security conference in Amsterdam, Holland, SRL researchers said that many OEMs are lying about these patches.
For the past two years, SRL researchers Karsten Nohl and Jakob Lell have analyzed the content of the security updates delivered by today's biggest Android OEMs.
The two discovered that some OEM vendors claim to deliver up-to-date security updates, but many skip installing some patches on users' devices, for unknown reasons.
"Our large study of Android phones finds that most Android vendors regularly forget to include some patches, leaving parts of the ecosystem exposed to the underlying risks," the SRL team said today in a blog post accompanying their HackInTheBox presentation slides.
Some device vendors are worse than others, skipping four or more patches, but claiming to have up-to-date devices.
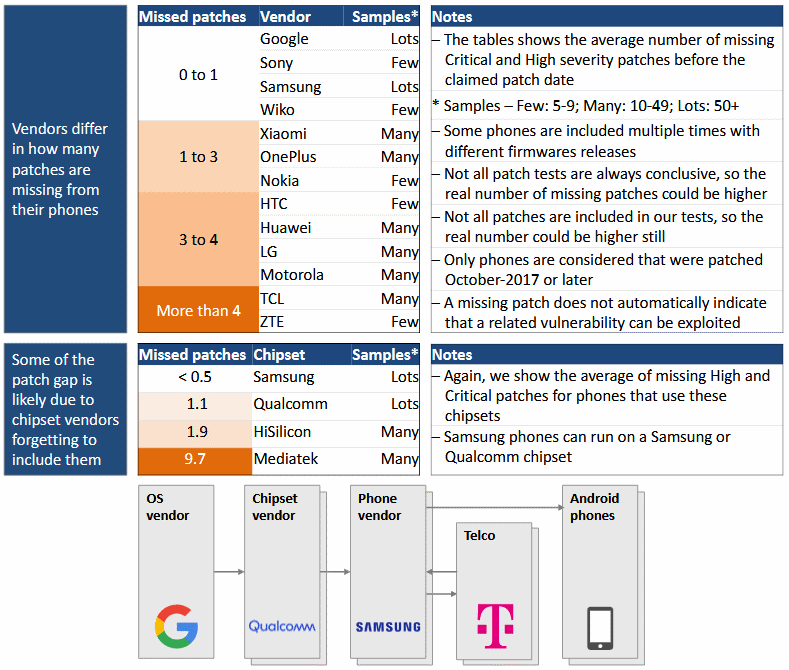
Some chipset vendors are also to blame for the patch gap
According to Nohl and Lell, one reason for the tardiness or gap in patch delivery may be the chipset (CPU) providers, where researchers noticed that one specific company —Mediatek— was often lagging 9-10 patches behind.
This, in turn, created a bottleneck for many OEM providers, who were ready to ship the Android OS-specific patches, but did not have the firmware-related fixes from the chip vendor.
Because these hardware-level fixes are accounted for in the Android security bulletins, this created situations where OEMs delivered updates claiming to have a "security patch level" but they were actually missing some of the patches for that "level."
But not all missing patches can be attributed to lazy chipset vendors, and in some cases, the missing patches were specific to the OEM slacking off.
The SRL team has released an app on the Google Play Store named SnoopSnitch that helps users analyze their own device and tells them what patches are missing and if their device is truly up-to-date as the "security patch level" may say in the settings section.
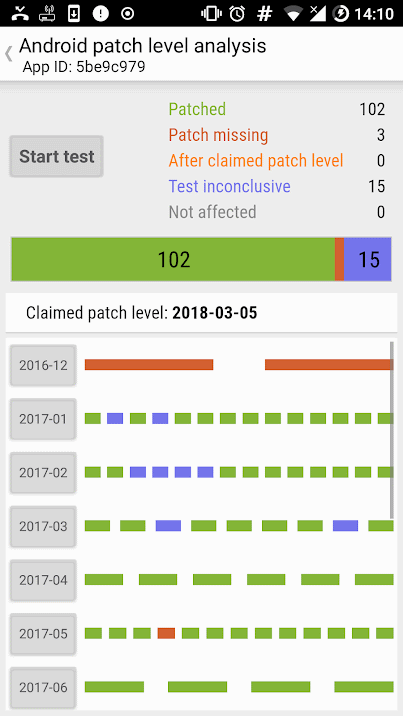
Image credits: Claudia Rahanmetan, Security Research Labs
Red Report 2026: Why Ransomware Encryption Dropped 38%
Malware is getting smarter. The Red Report 2026 reveals how new threats use math to detect sandboxes and hide in plain sight.
Download our analysis of 1.1 million malicious samples to uncover the top 10 techniques and see if your security stack is blinded.










Comments
GT500 - 7 years ago
ASUS has a great solution for this problem. They just never say when they're publishing security patches, that way they can wait 4-6 months between updates and never miss a release date.
BTW: Never buy an ASUS phone, unless you enjoy walking around with Swiss Cheese in your pocket. And I say that as the "proud" owner of 2 ASUS phones.
Exnor - 7 years ago
"ASUS has a great solution for this problem. They just never say when they're publishing security patches, that way they can wait 4-6 months between updates and never miss a release date.
BTW: Never buy an ASUS phone, unless you enjoy walking around with Swiss Cheese in your pocket. And I say that as the "proud" owner of 2 ASUS phones."
Oh i see i have a fellow Asus owner... what was the model that made you regret? Mine was the Zenfone 2 ZE551ML... the very 1st week i've got it i got a dead logic board...
GT500 - 7 years ago
I didn't pay enough attention to my ZenFone 2, so for me it was my ZenFone 3 Deluxe ZS570KL. For the first 8 months they released security patches every 3-4 months, then they moved to every 6 months. They also don't seem to care about people bringing up security issues or their lack of firmware updates on their official forums (the thing is full of people complaining). I'm hoping that when they release their Android 8 update for the phone it will get some more frequent patches, but that just depends on how much of the patching ASUS has to do on their own (if it's any at all then that will probably be the last update for the phone).
Exnor - 7 years ago
"I didn't pay enough attention to my ZenFone 2, so for me it was my ZenFone 3 Deluxe ZS570KL. For the first 8 months they released security patches every 3-4 months, then they moved to every 6 months. They also don't seem to care about people bringing up security issues or their lack of firmware updates on their official forums (the thing is full of people complaining). I'm hoping that when they release their Android 8 update for the phone it will get some more frequent patches, but that just depends on how much of the patching ASUS has to do on their own (if it's any at all then that will probably be the last update for the phone)."
If Asus does the same with the Zenfone 3 as they did with the Zenfone 2 you will never get Android 8.... Just take a look at their forums for the Zenfone 2.
It's really sad because Asus is quite good if not one of the best in the market for other type of devices (motherboards, Networking, etc...), but for some reason they really let the consumer/customer down with their smartphones :( .
To be fair, for the price, the Hardware is quite good imho. The problem appears to be assembly quality control and of course lack of software updates and support.
Exnor - 7 years ago
Asus should be on the list... their software update is a bad joke... the Hardware is good for the money (actually was.. now it's overpriced like the rest).
GT500 - 7 years ago
The list shows vendors who are lying about security patches, or who are making mistakes and failing to publish patches they have included in their patch notes. ASUS gets around this by simply not mentioning what security updates they are including, if they even bother to include security updates at all (right now they are waiting 6-month between security patches for the ZenFone 3 Deluxe ZS570KL, and I haven't checked on my ZenFone 2 in a couple of years but I think they stopped patching it before I got the ZenFone 3).
Exnor - 7 years ago
"The list shows vendors who are lying about security patches, or who are making mistakes and failing to publish patches they have included in their patch notes. ASUS gets around this by simply not mentioning what security updates they are including, if they even bother to include security updates at all (right now they are waiting 6-month between security patches for the ZenFone 3 Deluxe ZS570KL, and I haven't checked on my ZenFone 2 in a couple of years but I think they stopped patching it before I got the ZenFone 3)."
Last patch on the Zen2 is about to reach 1 year old... and i don't think users like me will ever get any more updates/patches or whatever for the device ....
Exnor - 7 years ago
.
J.Aza - 7 years ago
Honestly, if you're savvy enough to be on here reading you shouldn't be beholden to OEMs for your patches. Root and get your patches from "the community". You may have to pick a custom rom (though most every phone has a rooted "custom" rom that's damned close to stock) but if it's a phone w/ active development you'll get updates and patches baked in.
(xda-developers.com in the forums in case you didn't know...)