In trays of printed paper, a new service called Printeradvertising.com was launched that states that it can print a viral advertising campaign to every connected printer in the world.
While this is an overstatement, the service did start out with a bang when Andrew Morris, founder of security company Grey Noise, detected a mass printer spam campaign promoting the service connecting to his company's honeypots.
.@GreyNoiseIO just detected someone (specifically 194.36.173[.]50) spraying the entire Internet with print commands for this document advertising a world-wide printing service, similar to HackerGiraffe's PewDiePie printer hack and Weev's swastika printer hack. pic.twitter.com/Ge0kebMzI7
— Andrew Morris (@Andrew___Morris) December 2, 2018
Morris told BleepingComputer that at least sixty distinct Grey Noise honeypot detected connections coming from IP address 194.36.173.50 that were trying to send print jobs. Bad Packets Report and Phishing AI state that this IP address belongs to a subnet known for malicious activity including phishing kits, C2 servers, and possibly malware such as Lokibot.
So @bad_packets says ASN 44685 full of cybercrime. Is he right?
— Phishing AI (@PhishingAi) November 22, 2018
Let's take a look at 194.36.173.0/24 current state
(only active campaigns)
On 194.36.173.6 we have a malware C2 server with multiple panels.
cc: @malwrhunterteam @JAMESWT_MHT @nullcookies @SteveD3 @thepacketrat pic.twitter.com/MgjnllEeQ4
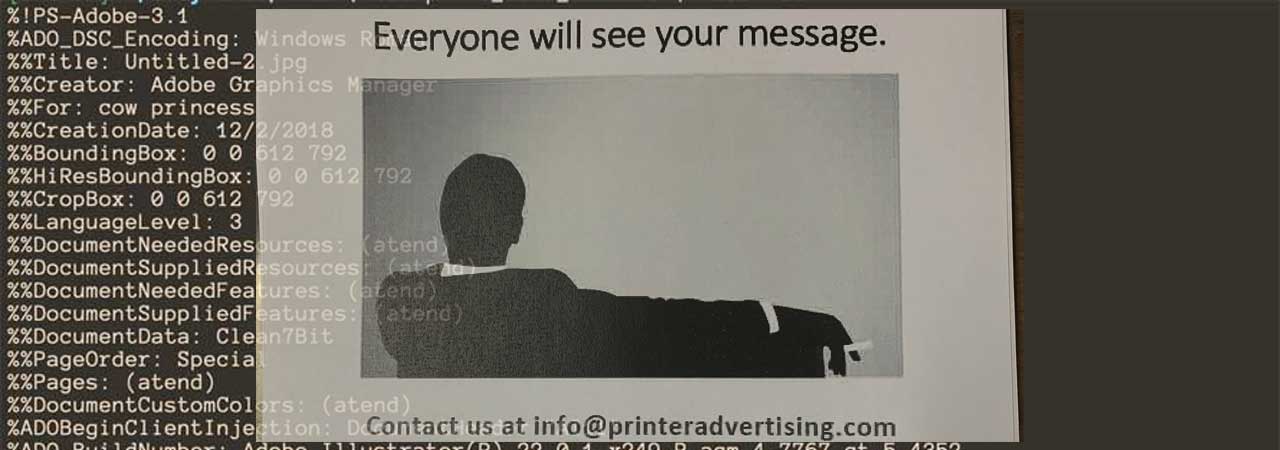
When the spam print job is sent, it does so using raw PCL (Printer Command Language) that instructs the printer how to format and print the document.
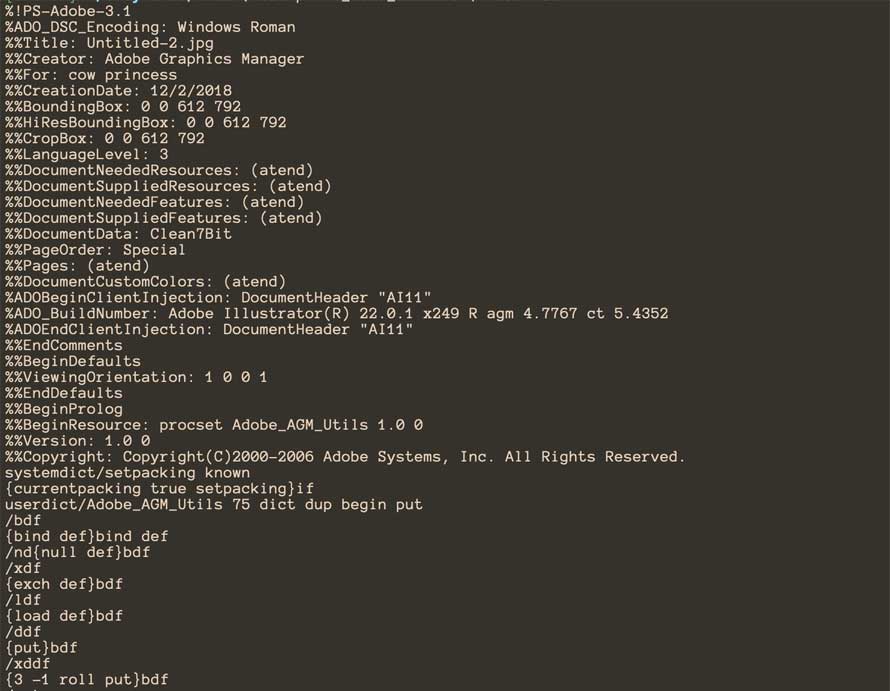
When successful, it would cause the printer to print an advertisement for the printeradvertising.com site as shown below.

(Source: Technobuffalo)
The full text of this advertisement is:
Guerrilla marketing experts - printeradvertising.com
Secure your spot in the most viral ad campaign in history.
We have the ability to reach every single printer in the world!
Reservations are limited.
According to a tweet from someone named @printerads that claims to run the site, this campaign was meant to see if anyone was interested in actually using the service. If people are interested, they would build out a service to support more printing protocols.
We're currently mostly trying to see if anyone's interested, if people actually want to buy this we'll build a web platform with support for more printing protocols.
— printeradvertising (@printerads) December 2, 2018
In response to questions from BleepingComputer, Printeradvertising has stated that this is a real service, that they on offering the service for $250 and have received over 600 emails today. Launching a service like this is no doubt illegal as they are performing unauthorized activity on someone else devices.
Strangely, the printeradvertising.com site has URLs to an Australian security consultant named Simon Smith, which indicates that this may be an extensive trolling campaign.
Smith had told BleepingComputer that he has received numerous death threats and calls from around the world due to this printer spam. Smith has also posted this statement on LinkedIn:
The person behind the Printeradvertising campaign, though, continues to claim their are Smith and signs their emails as "eVestigator®, Simon Smith".
This type of activity is not new. Other printer spam is currently being sent that includes ones asking people to subscribe to PewDiePie's YouTube channel and spam for the L0de Radio Hour.
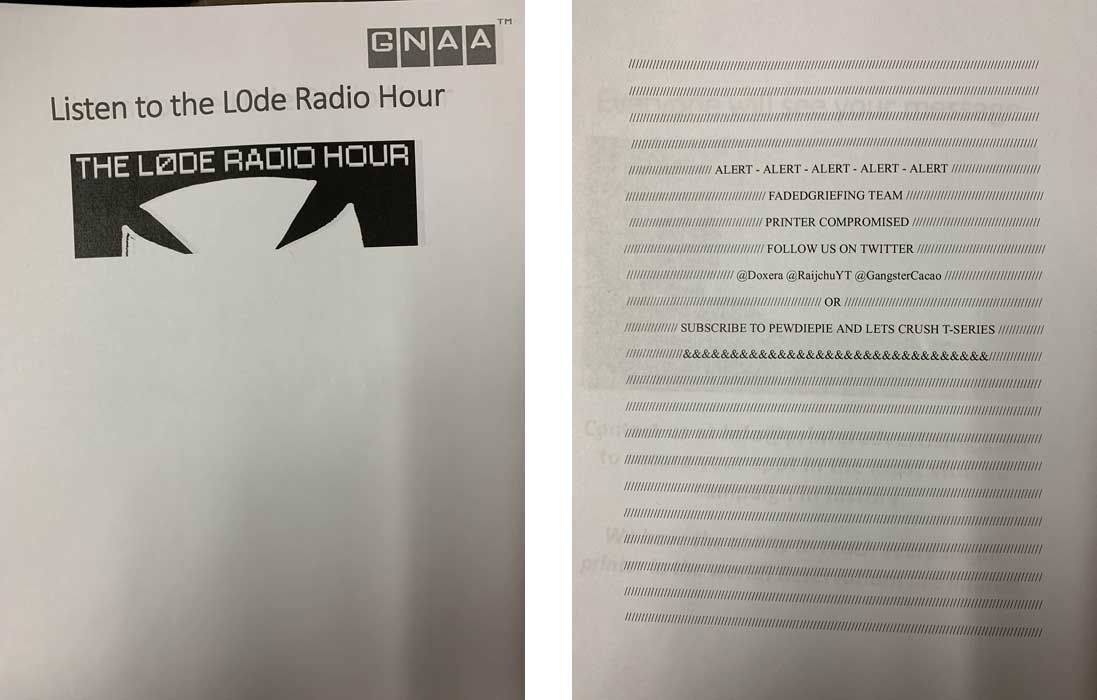
The owner of the L0de Radio Show contacted BleepingComputer and issued this statement:
"I deny any involvement in these printer scam campaigns and disavow these actions. I've taken down my YouTube channel and made my twitter account protected so as not to benefit from them and am directing visitors to a charitable organization."
Printers should not be connected to the Internet
In order to prevent this type of mischief, network enabled printers should never be connected to the Internet. Allowing them to do so only allows malicious actors to send any type of print document to your network, including pornography that could land you in trouble.
While many ISPs block the TCP ports associated with printer daemons, many do not. According to Shodan.io, there are over 13,000 Internet printers connected through ISPs such as Comcast, Verizon Fios, Spectrum, and AT&T.
If it is absolutely necessary to allow remote users to print to network printers in your organization, you should instead place them behind firewalls and require users to VPN into the network to use the internal resources.
Update 12/3/18 9:27 PM EST: Updated to include statement posted by Simon Smith on LinkedIn.
Update 12/3/18 9:27 PM EST: Updated with responses from an email with Printeradvertising.
Update 12/4/18 4:39 PM EST: Updated with statement from L0de.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.










Comments
SimonSmith - 7 years ago
Hi all. This is Simon Smith from eVestigator. After receiving thousands of calls I would like to assure people that neither I or my company have anything to do with this disgusting website. We have reported it to the FBI and are simply named on the site. Prior to this the cyber criminals DDoS'd thousands of servers placing our name in a spoofed user agent and each time they harrass and stalk us by taunting and sending SMS threatening that they are continuing. I am a cyber crime investigator and find cybercriminals successfully. These people are obviously trying to stop me from doing what I do, however they are harming many others and leaving traces behind. I have been stalked and sent death threats now for two years simply for succeeding in this industry. I strongly recommend to report any IP address to the FBI as I have done, as they are using my name and company on a website I have nothing to do with for illegal purposes. Naturally I will also be investigating them and doing whatever it takes to lock these people up. It is a very poor and desperate campaign by unskilled people that are hurting innocent people and also directly attacking one of the very few people that helps victims of cybercrime when the police cannot fully investigate cases. It is a sad state of events. I have answered as many people as possible and urge anybody who takes a non evidence view of the privately registered domain having any ownership to me, I'd like to know about it. It is now both a civil and criminal matter.