
A new wave of North Korea's 'Contagious Interview' campaign is targeting job seekers with malicious npm packages that infect dev's devices with infostealers and backdoors.
The packages were discovered by Socket Threat Research, which reports they load the BeaverTail info-stealer and InvisibleFerret backdoor on victims' machines, two well-documented payloads associated with DPRK actors.
The latest attack wave uses 35 malicious packages submitted to npm through 24 accounts. The packages have been downloaded over 4,000 times in total, and six of them remain available at the time of writing.
Several of the 35 malicious npm packages typosquat or mimic well-known and trusted libraries, making them especially dangerous.
Notable examples of those are:
- react-plaid-sdk, reactbootstraps
- vite-plugin-next-refresh, vite-loader-svg
- node-orm-mongoose
- jsonpacks, jsonspecific
- chalk-config
- node-loggers, *-logger
- framer-motion-ext
- nextjs-insight
- struct-logger, logbin-nodejs
Victims, typically software engineers and developers, are led to download these packages by North Korean operatives posing as recruiters, requesting job candidates to work on a test project.
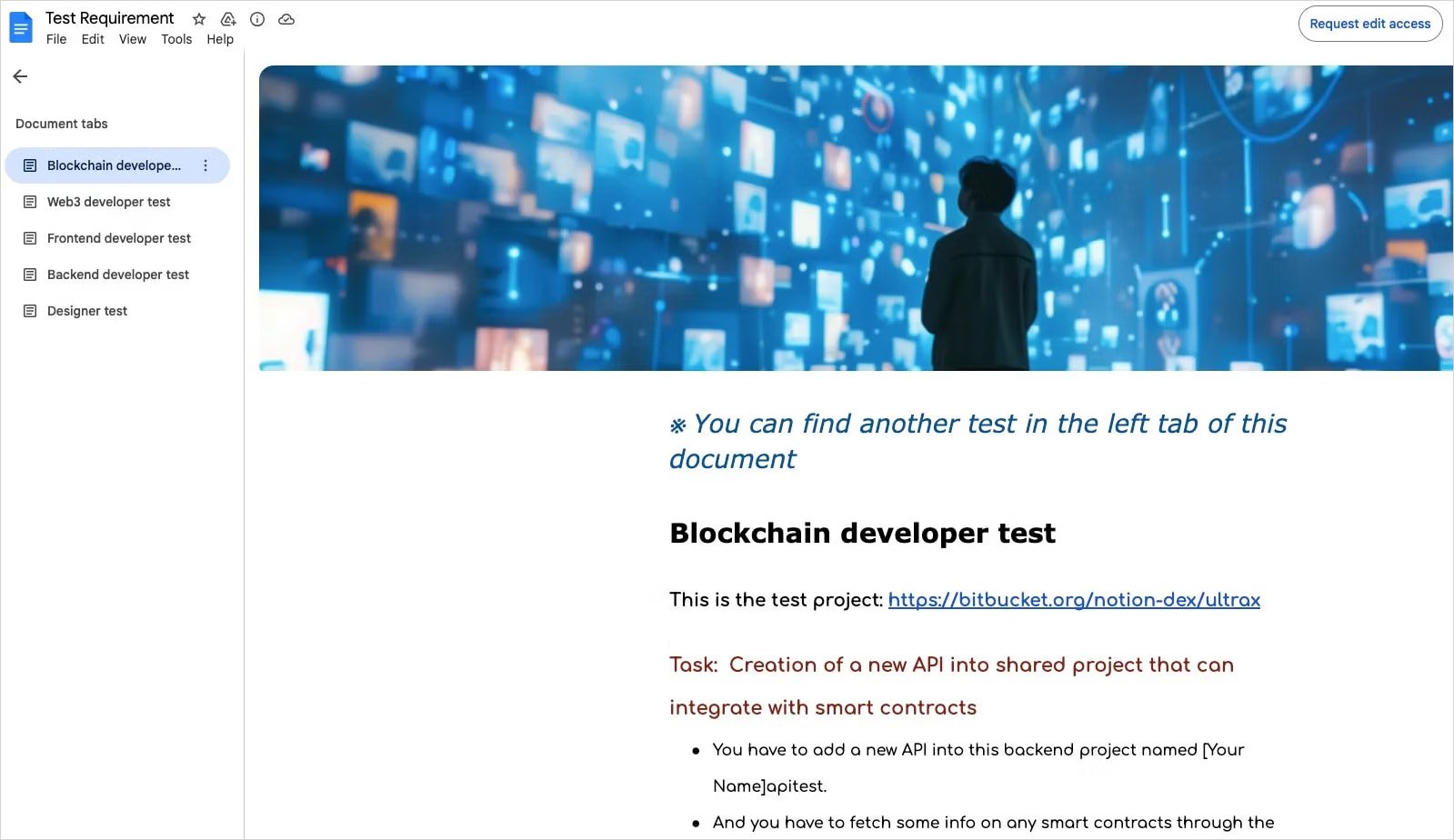
"Posing as recruiters on LinkedIn, the North Korean threat actors send coding "assignments" to developers and job seekers via Google Docs, embed these malicious packages within the project, and often pressure candidates to run the code outside containerized environments while screen-sharing," explains Socket.
Source: Socket
The assignments are hosted on Bitbucket and disguised as legitimate tests, but in reality, they trigger an infection chain that drops multiple payloads on the target's computer.
The first stage is HexEval Loader, hidden in the npm packages, which fingerprints the host, contacts the threat actor's command-and-control (C2) server, and uses 'eval()' to fetch and execute the second stage payload, BeaverTail.
BeaverTail is a multi-platform info-stealer and malware loader that steals browser data, including cookies and cryptocurrency wallets, and loads the third stage, InvisibleFerret.
InvisibleFerret is a cross-platform persistent backdoor delivered as a ZIP file, giving the attackers deeper, ongoing access to the victim's system with remote control, file theft, and screen-shooting capabilities.
Finally, the attackers drop a cross-platform (Windows, macOS, Linux) keylogger tool that hooks into low-level input events and performs real-time surveillance and data exfiltration.
This keylogger was only associated with one of the npm aliases used in the campaign, so it might be deployed only on select high-value targets.
.jpg)
Source: Socket
Software developers approached with lucrative remote job offers should treat these invitations with caution and always run unknown code in containers or virtual machines instead of executing it on their OS.
Last March, North Korean hackers Lazarus were caught submitting another set of malicious packages on npm, so this is an ongoing risk.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.










Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now