The multifunctional Emotet botnet malware was the most prevalent email-based threat in the first three months of the year, showing it is among the top choices for cybercriminals.
Telemetry data from Proofpoint antivirus company indicates that Emotet has become the go-to botnet service to spread malware across the world, as it was the primary payload detected on protected computers.
Emotet started off as a banking malware and developed into a tool that can send out spam messages and distribute other threats on the systems it compromises.
Statistics gathered by Proofpoint from the computers it protects in the first quarter of the year shows that 61% of malicious payloads delivered via email were botnets, all detected as Emotet.
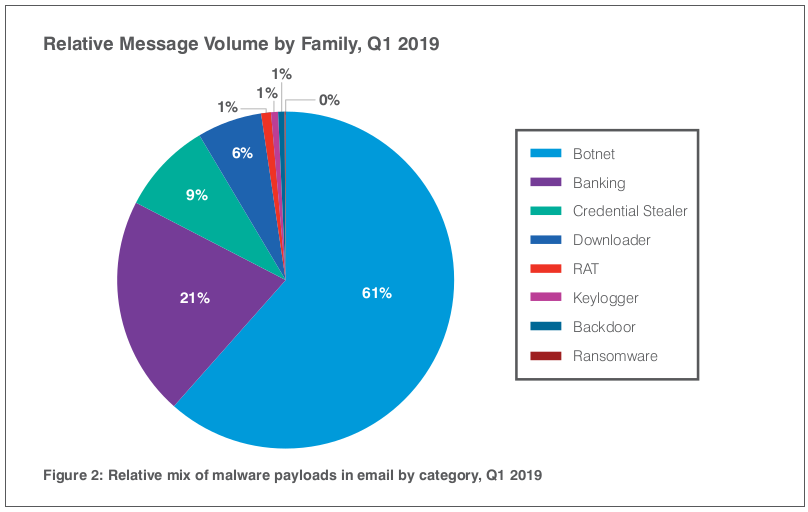
Other threats spread over malicious emails and detected by Proofpoint are banking trojans, which came into a distant second place, credential stealers, downloaders, and remote access trojans (RATs).
"Banking Trojans made up only 21% of malicious payloads in Q1," informs the report, adding that along with Emotet, the two threats accounted for 82% of all email-borne malware.
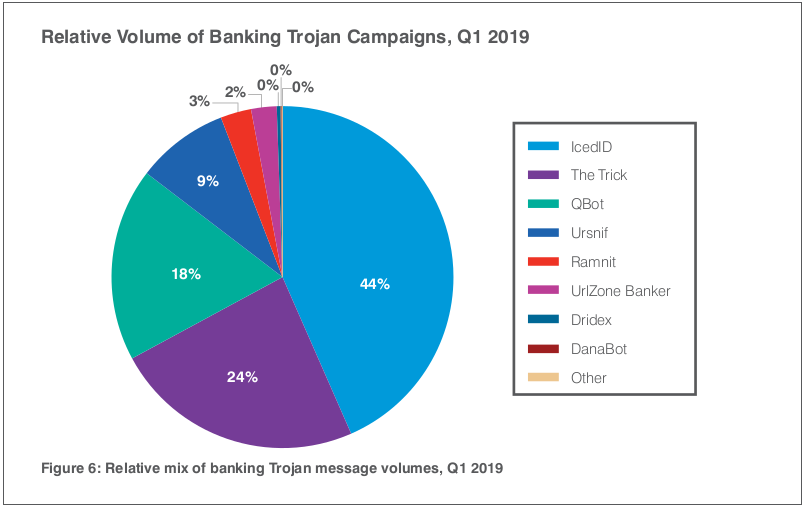
The most detected threats related to banking activity were IcedID, The Trick and Qbot. Together, they represent 85% of the payloads pushed over email in the first three months of 2019.
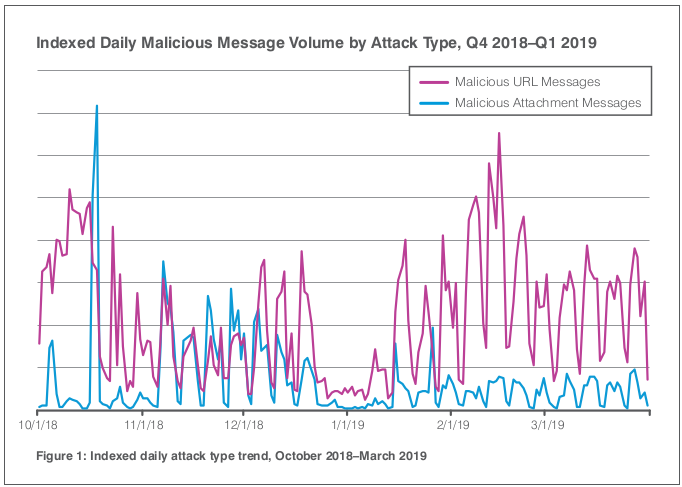
Email is the main method for delivering malware, which can come either as an attachment to the message or via download link included in the email body.
According to Proofpoint's statistics, attacks that rely on malicious URLs have recorded significant growth compared to those that delivered as an attachment.
"Malicious URLs in emails outnumbered malicious attachments by roughly 5 to 1 for Q1, up 21% quarter over quarter and 180% vs. Q1 2018," reads the report.
This information is in a context where the volume of messages remained relatively the same compared to the previous quarter.
The prevalence of malicious links present in the email body is also an effect of the Emotet botnet increased activity, say the researchers.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.










Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now