
Click above to see the full image.
When you click on the links in the ransom note you will be brought to the CryptoLocker Decryption Software site where you can learn how to purchase the decrypter. Like other infections, this site will require you to send the specified amount of bitcoins to a particular address and then input the transaction ID to verify payment. Once payment has been established, you will be offered a decryption program that you can download to decrypt your files. The decryption site also offers a customer support form, frequently asked questions section, and the ability to decrypt one file for free.

Click above to see the full image.
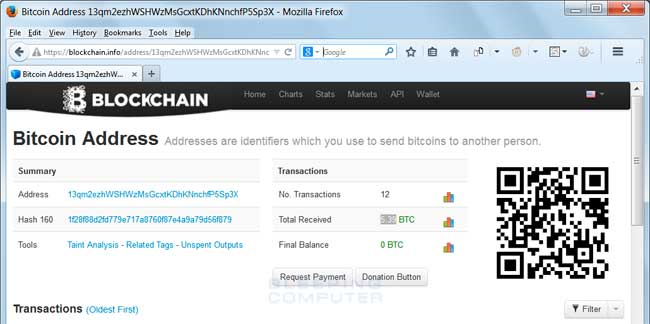
At this time, the ransom is 1.8 BTC, which is equivalent to 1,000 AUD. Strangely this infection uses a static bitcoin address of 13qm2ezhWSHWzMsGcxtKDhKNnchfP5Sp3X to receive payments. The address currently shows 5.39 BTC having been sent to this address.
Click above to see the full image.
Thankfully, this variant does not delete Shadow Volume Copies, which can be used to recover some of your files. Information on how to restore files from Shadow Volume Copies using Shadow Explorer can be found in the original CryptoLocker guide.
To remove this infection, you will need to remove the following files and registry keys:
C:\ProgramData\<random>.exe C:\ProgramData\<random>.html C:\Users\All Users\<random>.exe C:\Users\All Users\<random>.html C:\Users\User\AppData\Local\Temp\etilqs_qZAdaD7Y2gtuzMi HKCU\Software\Microsoft\Windows\CurrentVersion\Run\<random> C:\ProgramData\<random>.exeUpdate: 9/9/14 - This ransomware is being titled TorrentLocker via various organization.




 Back to top
Back to top












